ShinyHunters Breaches EU Commission: 350GB Data Exposed

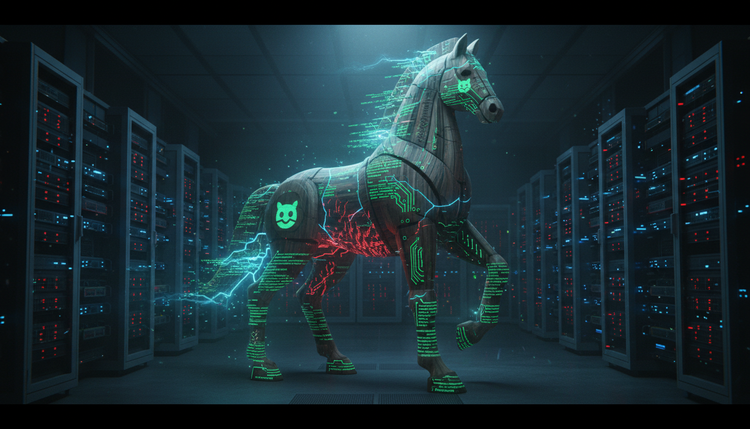
The European Union's digital infrastructure has suffered a catastrophic breach that exposes fundamental vulnerabilities in even the most security-conscious government institutions. On 24 March 2026, the notorious ShinyHunters cybercriminal group successfully compromised multiple EU institutions, including the European Commission, ENISA (the EU Agency for Cybersecurity), and the Directorate-General for Digital Services, exfiltrating over 350GB of highly sensitive operational data.
This breach strikes at the heart of European digital sovereignty. The compromise of ENISA—the very agency responsible for coordinating cybersecurity across the EU's 27 member states—creates an unprecedented crisis of confidence in the bloc's ability to protect critical digital infrastructure.
The Scale of Compromise: Beyond Initial Disclosures
Whilst the European Commission confirmed the cyberattack on 27 March 2026, stating that threat actors breached their cloud infrastructure hosting Europa.eu websites, the actual scope appears far more extensive than initially disclosed. According to security researchers at International Cyber Digest, ShinyHunters has compromised not just the Commission, but multiple interconnected EU institutions.
The stolen data represents a comprehensive breach of EU operational security. Firstly, complete email servers with attachments have been exfiltrated, potentially exposing years of sensitive communications. Secondly, a full Single Sign-On (SSO) user directory containing authentication credentials for EU staff has been compromised. Additionally, DKIM signing keys (cryptographic signatures that authenticate official EU communications) have been stolen, alongside AWS configuration snapshots revealing detailed cloud infrastructure layouts.
The breach also encompasses data from NextCloud collaboration platforms and the Athena military financing mechanism. Internal administrative URLs have been exposed, potentially providing roadmaps for future attacks. ShinyHunters has already released over 90GB of this stolen data on their dark web leak site, with the remaining 260GB being held as leverage—a common extortion tactic in modern cybercrime.
"The leak site describes the cache as containing 'data dumps of mail servers, databases, confidential documents, contracts, and much more sensitive material.'" This represents one of the most significant breaches of EU institutions in recent memory.
Critical Implications: Authentication and Trust Compromised
The exposure of SSO credentials and DKIM signing keys creates immediate and severe security implications. Attackers can now potentially impersonate EU officials with cryptographically valid communications, making fraudulent emails appear completely legitimate. This capability undermines the entire trust framework upon which digital governance relies.
The AWS configuration data provides detailed insights into the EU's cloud infrastructure architecture. These blueprints could enable sophisticated attackers to identify additional vulnerabilities or plan future intrusions. Given that modern government operations increasingly rely on cloud services, this exposure creates long-term security challenges that extend beyond immediate credential rotation.
Perhaps most concerning is the compromise of ENISA itself. As the EU's cybersecurity coordination body, ENISA holds sensitive information about security vulnerabilities, incident response procedures, and defensive strategies across member states. This meta-level breach potentially exposes not just current security measures but also the EU's cybersecurity roadmap and strategic planning.
Immediate Protective Measures Required
EU institutions must implement emergency response protocols immediately. All DKIM signing keys and SSL certificates require immediate revocation and reissuance. However, this process itself presents challenges—how do you securely communicate new authentication protocols when the authentication system itself has been compromised?
For EU Staff and Contractors
- Immediately rotate all passwords across all systems, not just those obviously compromised
- Enable additional multi-factor authentication factors beyond standard two-factor authentication
- Assume all previous communications may be compromised and establish new secure channels
- Be extremely vigilant for social engineering attempts using leaked internal information
For Member State Governments
- Review and strengthen authentication protocols for any systems integrating with EU platforms
- Implement additional monitoring on all EU-connected systems for anomalous activity
- Establish alternative communication channels for sensitive EU coordination
- Conduct immediate security audits of shared infrastructure and data exchanges
For Private Organisations and Citizens
- Exercise extreme caution with any communications claiming EU origin
- Verify all EU communications through alternative channels before taking action
- Monitor for phishing attempts using sophisticated knowledge from leaked data
- Consider any EU-related credentials or integrations as potentially compromised
Strategic Context: An Escalating Threat Landscape
This breach represents a significant escalation in ShinyHunters' operational ambitions. The group, active since 2020, has previously targeted major corporations including Salesforce partners and telecommunications providers. However, directly attacking the EU's cybersecurity apparatus marks a new level of audacity and capability.
The timing is particularly concerning. Just months ago, ShinyHunters released 6.2 million Odido customer records for free, demonstrating their willingness to cause maximum damage when ransom demands aren't met. This pattern of escalation suggests that critical infrastructure and government institutions worldwide should prepare for increasingly sophisticated attacks from well-resourced cybercriminal groups.
Against this context, the breach raises fundamental questions about digital sovereignty and security architecture. If the EU's own cybersecurity agency can be compromised, what does this mean for smaller nations or private organisations with fewer resources? The incident arguably demonstrates that traditional perimeter-based security models are insufficient against determined, sophisticated adversaries.
Looking Forward: Rebuilding Trust in Digital Infrastructure
The immediate priority must be damage control and system hardening. However, this breach demands a fundamental reassessment of how critical digital infrastructure is secured. Zero-trust architectures, where no user or system is inherently trusted, may need to become the default rather than the exception.
EU institutions will need to rebuild trust through transparency about the breach's full scope and their remediation efforts. This process will likely take months or years, during which the EU's digital initiatives may face increased scrutiny and resistance.
Finally, this incident underscores the asymmetric nature of modern cyber warfare. A small group of criminals has successfully compromised institutions representing 450 million citizens and a €17 trillion economy. This David-versus-Goliath dynamic means that defensive strategies must evolve beyond traditional approaches to address the reality that attackers need only succeed once, whilst defenders must succeed every time.
Sources
- Security Affairs - ShinyHunters Claims European Commission Hack
- BleepingComputer - European Commission Data Breach
- Infosecurity Magazine - European Commission Cloud Breach
- International Cyber Digest - Breach Analysis
- Silicon Republic - ShinyHunters Claims Responsibility
- HackRead - 350GB Data Breach Details